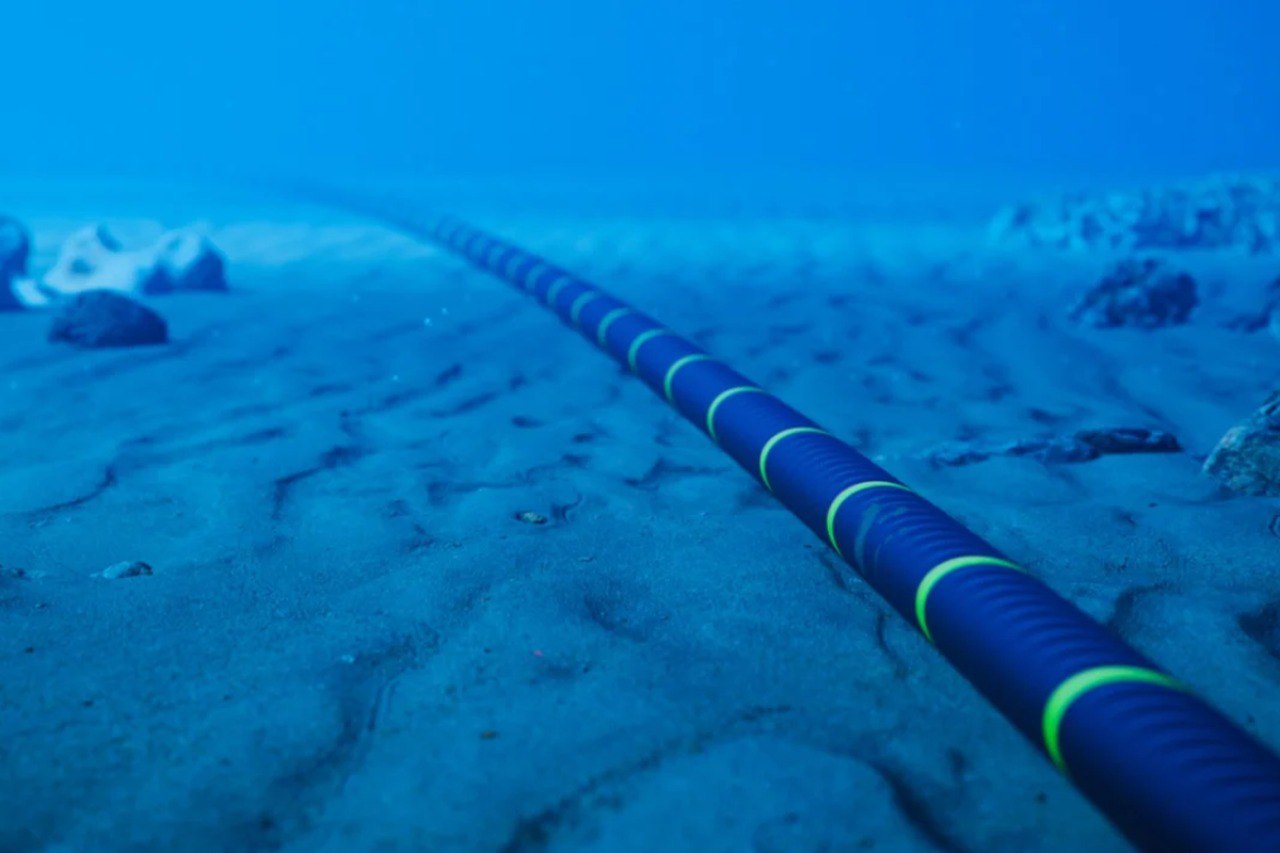
The vast majority of intercontinental global Internet traffic—upwards of 95 percent—travels over undersea cables across the ocean floor. These hundreds of cables, owned by combinations of private and state-owned entities, support everything from consumer shopping to government document sharing to scientific research on the Internet. The security and resilience of undersea cables and the data and services that move across them are an often understudied and underappreciated element of modern Internet geopolitics. The construction of new submarine cables is a vital part of the constantly changing physical topology of the Internet worldwide.
The submarine data cables are the root of the critical infrastructure of digital verse. Global digital communications are transmitted via a global cable network, including emails, zoom internet calls, flight bookings, financial transactions, etc. Every bit of this data travels through physical fiber optic cables laid in greater depths of the ocean bed. With the recent trend of virtual work, exponential growing use of cloud storage and launch of 5G internet, and incorporation of automation in public services and industrial production, the sustenance and wellbeing of humanity are even more dependent on the proper working of underwater cables, along with the redressal of jurisdictional issues over cables being laid in international waters.
Nature of Threat
Two types of atrocities threaten the underwater cables, i.e., physical and Digital.
Physical damage is the most common threat responsible for approximately 200 subsea cable faults each year, classified as accidental physical damage from shipping and commercial fishing or even from underwater seaquakes. Industry actors have the responsibility of mitigating these incidents. There are more significant concerns of malicious threats. There are two primary physical challenges, i.e., destruction or tapping, which include isolated piracy cases by adversaries like Russia. For instance, the Losharik spy submarine, before a tragic fire in 2019 decommissioned, could likely map or destroy deep-sea cables. Several plausible objectives destroying a cable might be achieved: obstructing government and military communication in the initial stages of the conflict, depriving internet access to specific populations, and disrupting the economy for geopolitical purposes.
Tapping the cables is a more subtle approach than destroying them. The data collected from tapping can be used for espionage, which could be executed in three different ways: installing backdoors during cable manufacturing, attacking landing stations onshore, and linking cables to land-based networks.
Digital Damage: cyber attacks such as hacking are the most common threat to network management systems used by private companies to regulate data traffic through cables. Any instance of hacking could transform into a ‘nightmare scenario’ that would enable hackers to take over the system’s sole control or admin rights. This superior control over the system could enable hackers to disrupt data traffic or execute a kill click eradicating wavelengths transmitting data. The current colonial pipeline and SolarWinds cyber attacks present a strong case for strengthening network management systems.
Bolstering Undersea Resilience
The multifaceted nature of the private ownership usage and vulnerabilities of subsea cables, international action would need to utilize various formats to be effective. The following steps can be adopted:
Ally Intelligence: The nation-states should conduct and facilitate bilateral or multilateral confidential dialogues to facilitate better real-time information sharing. The information can be used in threat assessment to formulate the best solution for addressing undersea threats. Joint naval exercises by ally nations to prevent any factor to disrupt the cables.
Promoting national risk assessment: although cables are managed, maintained, and secured by the private entities, governments are responsible for ensuring the thorough scrutiny of each project beforehand to avoid any security breaches. The authorities should ensure that cables are diverse enough to warrant resilience. For instance, ‘Team Telecom’ reviews the security implications of all undersea cables on US shores. The growing advancements in technology has enabled nations to establish underwater surveillance centers namely IUSS (integrated Undersea surveillance system) to ensure better monitoring of network cables and enhancing risk assessment.
Formulate National Monitoring and fixing capabilities: nation-states should cooperate to step up their C.I protection efforts by sharing threat assessments of vulnerabilities and developing crucial assets such as autonomous underwater drones and surveillance ships. Robust anti-contingency plans should be devised to deal with instances of significant breaks.
Revising international legal Framework: the present legal regime is merely a patchwork of different international conventions and customary laws, such as UNCLOS (United Nations Conventions on the Law of Sea), which fails to safeguard undersea cables. The lacunae in the Framework do not prohibit states from using underwater cables as legit targets during wartime, jeopardizing the socio-economic wellbeing of a large chunk of the war-affected population. There is a need to promote a more comprehensive and holistic legal regime.
The law enforcement authorities and other stakeholders should have a more holistic approach to cyber resilience to combat digital atrocities that are constantly plaguing the society such as ransomware attacks, banking and financial frauds and whistleblowing etc. While there is undoubtedly much more that can be done, these recommendations are intended to serve as a helpful starting point as the nations begin to consider how to collectively ensure that the protection of this critical infrastructure corresponds with their immense importance for global security, societies, and economies.
Author – Mr. Shrey Madaan, Research Associate, CyberPeace Foundation